Operational Enforcement Layer
Ambient Authorization
Authorization through live coherence, not through tokens, profiles, biometrics, or persistent identity artifacts.
Definition
Authorization-first for ambient systems
Ambient systems should not identify first and authorize later. They should authorize through live coherence.
In current systems, authorization is downstream of identity verification. A user, device, workload, or agent first becomes a managed entity, then receives permissions through policy. Ambient Authorization breaks with that order.
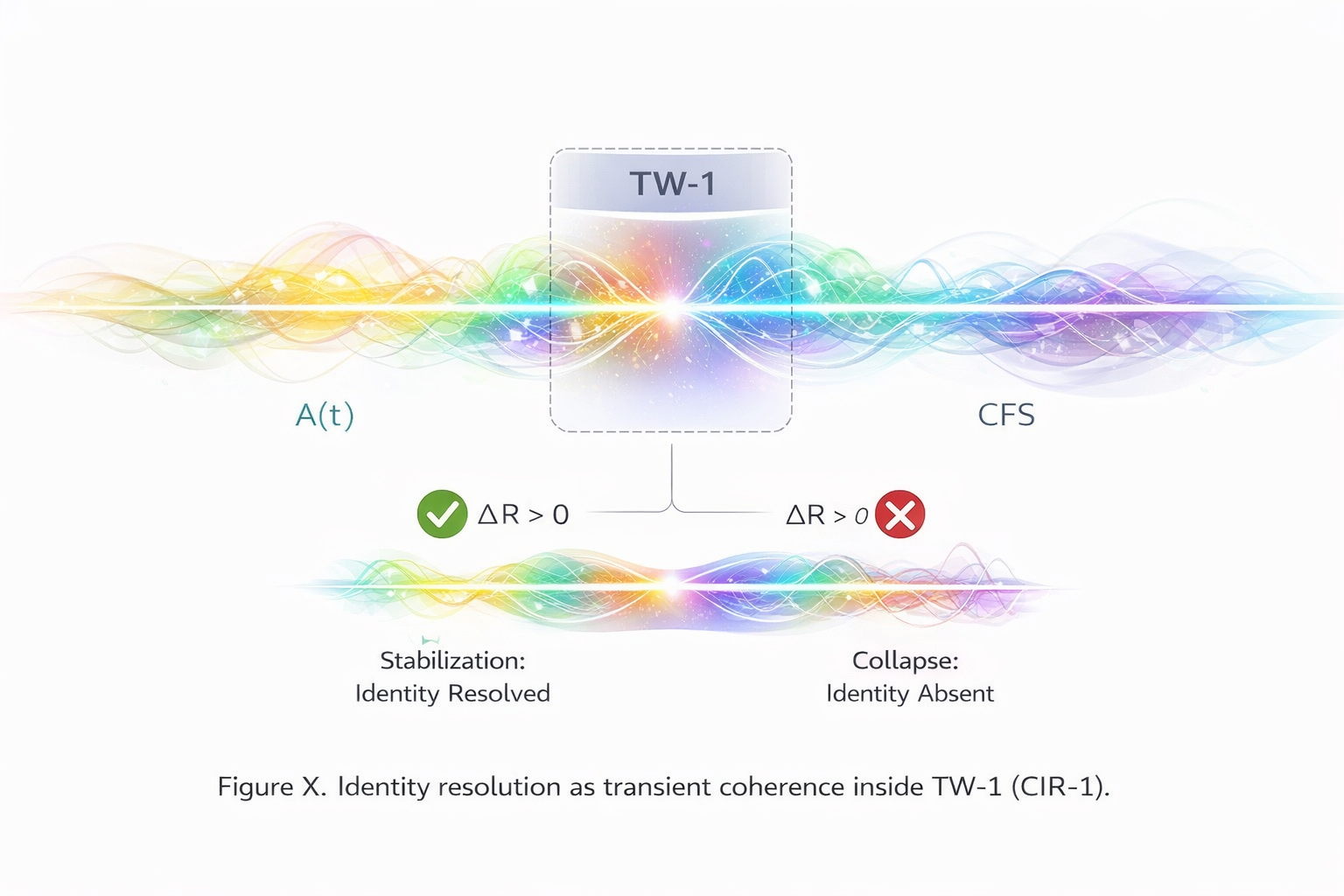
It defines access as a momentary field event: coherence resolves locally, authorization is granted or denied, and no persistent identity artifact needs to remain afterward.
Live authorization depends on aura dynamics, coherence, and reversible stress threshold inside a bounded window.
Current Landscape
The industry still authorizes through identity
Ambient computing, agentic AI, and zero trust are all expanding, but the market remains identity-first.
Current vendors improve governance for non-human identities, dynamic credentials, agent lifecycle control, and continuous verification. They do not remove the identity artifact from the authorization boundary.
NHI Governance
Machine and agent identities are discovered, managed, audited, and continuously revalidated.
Ambient Authentication
Human users are continuously recognized through passive context, behavior, or biometrics.
Zero Trust Extensions
Authorization remains downstream of identity, policy engines, endpoint posture, and managed trust signals.
The market has named ambient authentication and agent identity. It has not yet named authorization without identity artifacts.
Category Break
This is not authentication
Authentication-first systems
- Verify who or what something is
- Depend on tokens, certs, profiles, or templates
- Persist identities long enough to govern them
- Authorize after identity has already been established
- Improve trust by strengthening managed artifacts
Ambient Authorization
- Resolves permission directly in context
- Does not require a persistent identity object
- Leaves no replayable artifact after success or failure
- Authorizes through live coherence in TW-1
- Improves trust by avoiding identity residue altogether
Authentication asks who you are. Ambient Authorization asks what may now coherently happen.
Protocol Layer
AFS-1 in action
The operational core of Ambient Authorization is Aura Field Security: access resolves as live resonance between A(t) and CFS inside TW-1.
No token needs to be issued. No biometric template needs to be matched. No profile needs to be queried. Authorization succeeds only if coherence stabilizes locally inside the verification window.
Interactive Demo
See TW-1 in motion
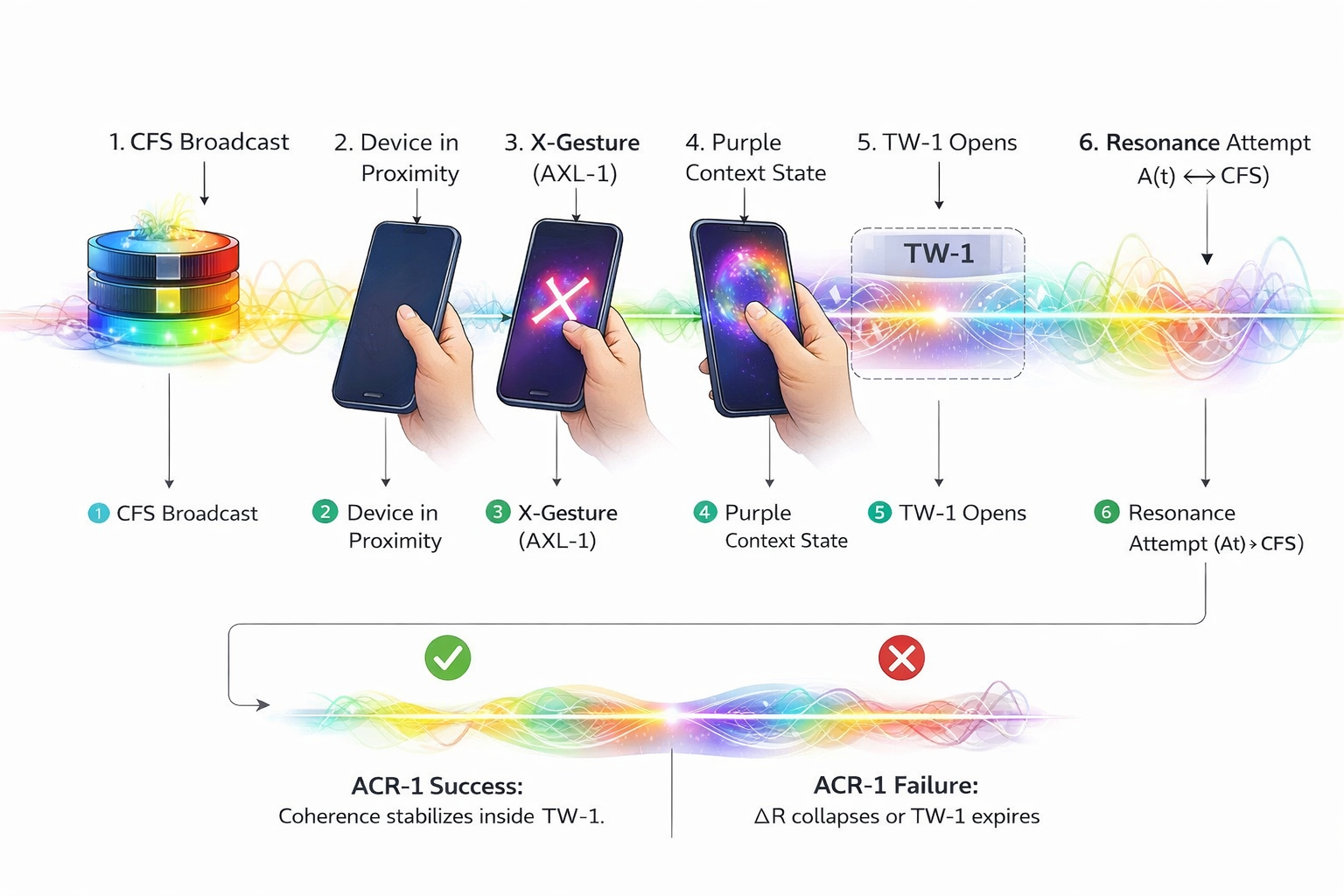
Ambient Authorization is not only a theory layer. A first TW-1 demo now illustrates how live coherence resolves inside a bounded verification window.
The demo simulates CFS broadcast, device proximity, gesture activation, Purple Context State, TW-1 opening, resonance evaluation, and residue collapse. It is a conceptual protocol visualization, not a credential-based login flow.
TW-1 Demo: ambientauthorization.com/tw-1-demo/
What it shows
Live authorization as a field event: coherence rises, TW-1 opens, resonance succeeds or fails, and no persistent identity artifact remains.
Why it matters
Current security systems visualize identity checks and policy gates. This demo visualizes authorization without identity-first artifacts.
Operational Characteristics
What makes this different in practice
Local resolution
Authorization resolves locally in the field, not by querying a central identity artifact first.
Zero persistent residue
After success or failure, no replayable identity object remains. Residue collapses with ΔR.
Non-replayable
A previous successful access event cannot simply be copied, replayed, or re-presented later.
Authorization-first
The system does not start by asking who you are. It starts by evaluating whether coherence is present now.
Canonical Placement
The enforcement layer inside the Raynor Stack
Ambient Authorization is not a standalone theory. It is the operational closure of a larger ambient architecture.
ambientcanon.com
Thermodynamic grammar, warm architecture, and the highest canonical abstraction layer.
ambientphone.com
The interface and hardware transition layer in which aura appears as human climate rather than data identity.
identitywithoutidentity.com
The philosophical and security break: why authorization must move beyond persistent identity artifacts.
ambientauthorization.com
The enforcement layer: how access, payment, privilege, and system decisions resolve through live coherence.
identitywithoutidentity.com explains why identity-first security must end. ambientauthorization.com explains how access resolves after it ends.
Implementation Direction
What this domain should develop next
This site should become the practical reference layer for coherence-based authorization in ambient systems.
Protocol specifications
TW-1, CFS broadcast, ΔR collapse, stolen-device rejection, and bounded field resolution.
Reference flows
Payments, device unlock, privileged action approval, and agent interaction without persistent identity artifacts.
Open demo layer
A TW-1 simulator or reference implementation that shows how authorization behaves in real time.
Source Layer